Hackers008 Archivesdiscovered a new way to remotely take control of your computer — all through the Google Chrome web browser.
A report from cybersecurity company SquareX lays out the new multifaceted cyberattack, which the firm has dubbed "browser syncjacking."
At the core of the attack is a social engineering element, as the malicious actor first must convince the user to download a Chrome extension. The Chrome extension is usually disguised as a helpful tool that can be downloaded via the official Chrome Store. It requires minimal permissions, further cementing its perceived legitimacy to the user. According to SquareX, the extension actually does usually work as advertised, in order to further disguise the source of the attack from the user.
Meanwhile, secretly in the background, the Chrome extension connects itself to a managed Google Workspace profile that the attacker has set up in advance. With the user now unknowingly signed into a managed profile, the attacker sends the user to a legitimate Google support page which is injected with modified content through the Chrome extension, telling the user they need to sync their profile.
When the user agrees to the sync, they unwittingly send all their local browser data, such as saved passwords, browsing history, and autofill information, to the hacker's managed profile. The hacker can then sign into this managed profile on their own device and access all that sensitive information.
The attack up to this point already provides the hacker with enough material to commit fraud and other illicit activities. However, browser syncjacking provides the hacker with the capability to go even further.
Using the teleconferencing platform Zoom as an example, SquareX explains that using the malicious Chrome extension, the attacker can send the victim to an official yet modified Zoom webpage that urges the user to install an update. However, the Zoom download that's provided is actually an executable file that installs a Chrome browser enrollment token from the hacker's Google Workspace.
After this occurs, the hacker then has access to additional capabilities and can gain access to the user's Google Drive, clipboard, emails, and more.
The browser syncjacking attack doesn't stop there. The hacker can take one further step in order to not just take over the victim's Chrome profile and Chrome browser, but also their entire device.
Through that same illicit download, such as the previously used Zoom update installer example, the attacker can inject a "registry entry to message native apps" by weaponizing Chrome’s Native Messaging protocol. By doing this, the attacker basically sets up a connection "between the malicious extension and the local binary." Basically, it creates a flow of information between the hacker's Chrome extension and your computer. Using this, the hacker can send commands to your device.
What can the hacker do from here? Pretty much anything they want. The attacker will have full access to the user's computer files and settings. They can create backdoors into the system. They can steal data such as passwords, cryptocurrency wallets, cookies, and more. In addition, they can track the user by controlling their webcam, take screenshots, record audio, and monitor everything input into the device.
As you can see, browser syncjacking is nearly completely unrecognizable as an attack to most users. For now, the most important thing you can do to protect yourself from such a cyberattack is to be aware of what you download and only install trusted Chrome extensions.
Topics Cybersecurity Google
 Trump praises storm response as historic disaster unfolds in Houston
Trump praises storm response as historic disaster unfolds in Houston
 The Enlightenment Is Like a Centaur—and We Must Kill It!
The Enlightenment Is Like a Centaur—and We Must Kill It!
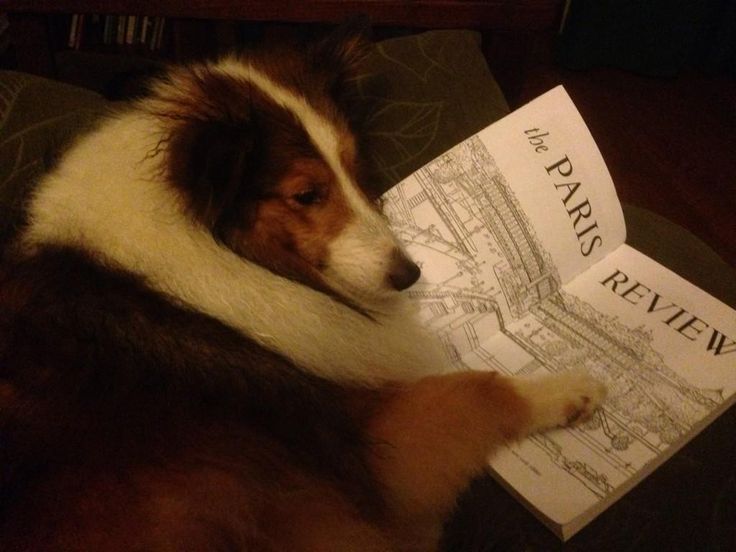 #ReadEverywhere, All Summer Long
#ReadEverywhere, All Summer Long
 The Candor of Tourists
The Candor of Tourists
 NYT Connections Sports Edition hints and answers for January 28: Tips to solve Connections #127
NYT Connections Sports Edition hints and answers for January 28: Tips to solve Connections #127
 An Appreciation of Tove Jansson
An Appreciation of Tove Jansson
 The Candor of Tourists
The Candor of Tourists
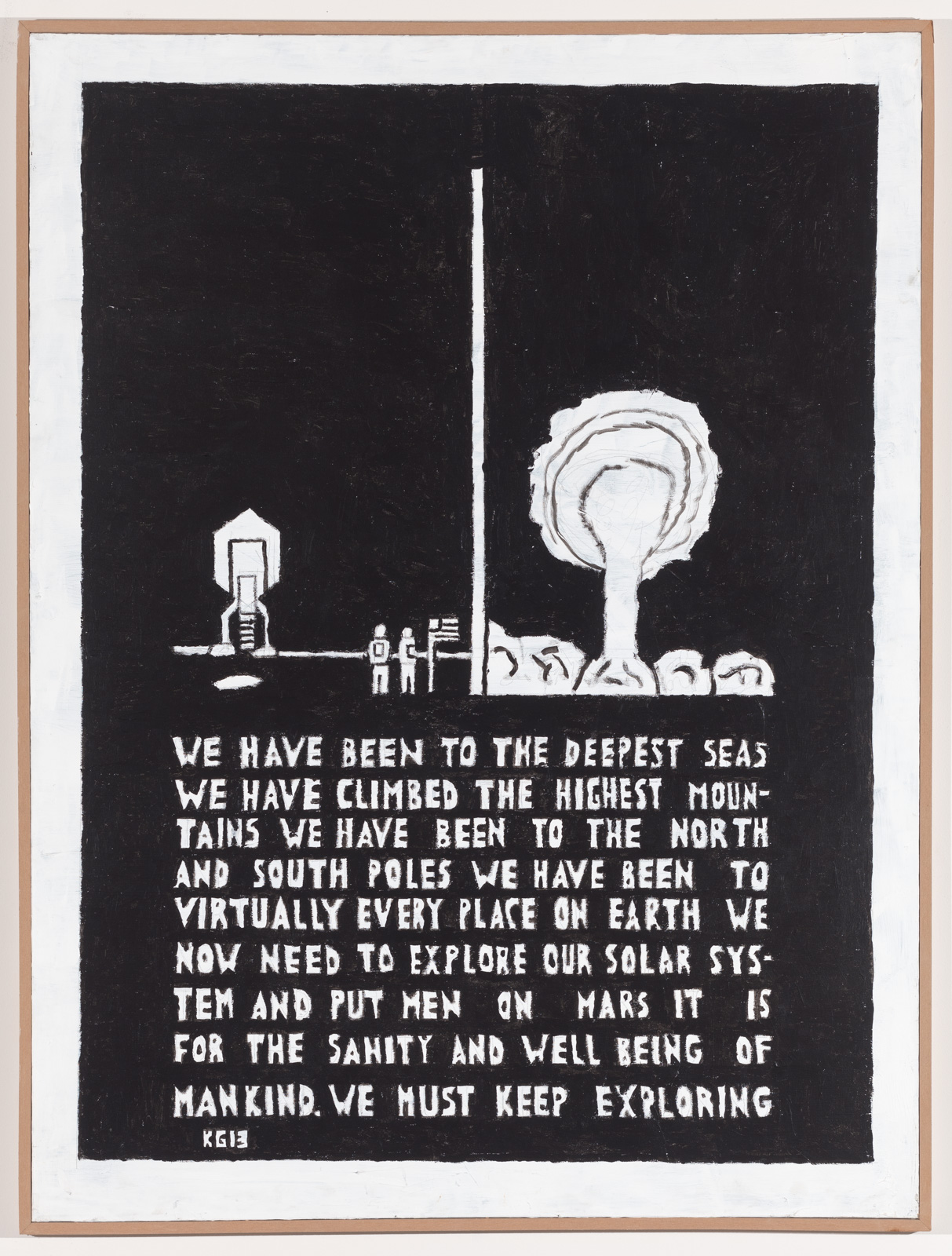 Ken Grimes’s Outsider Art Searches Restlessly for Alien Life
Ken Grimes’s Outsider Art Searches Restlessly for Alien Life
 Greenpeace activists charged after unfurling 'Resist' banner at Trump Tower in Chicago
Greenpeace activists charged after unfurling 'Resist' banner at Trump Tower in Chicago
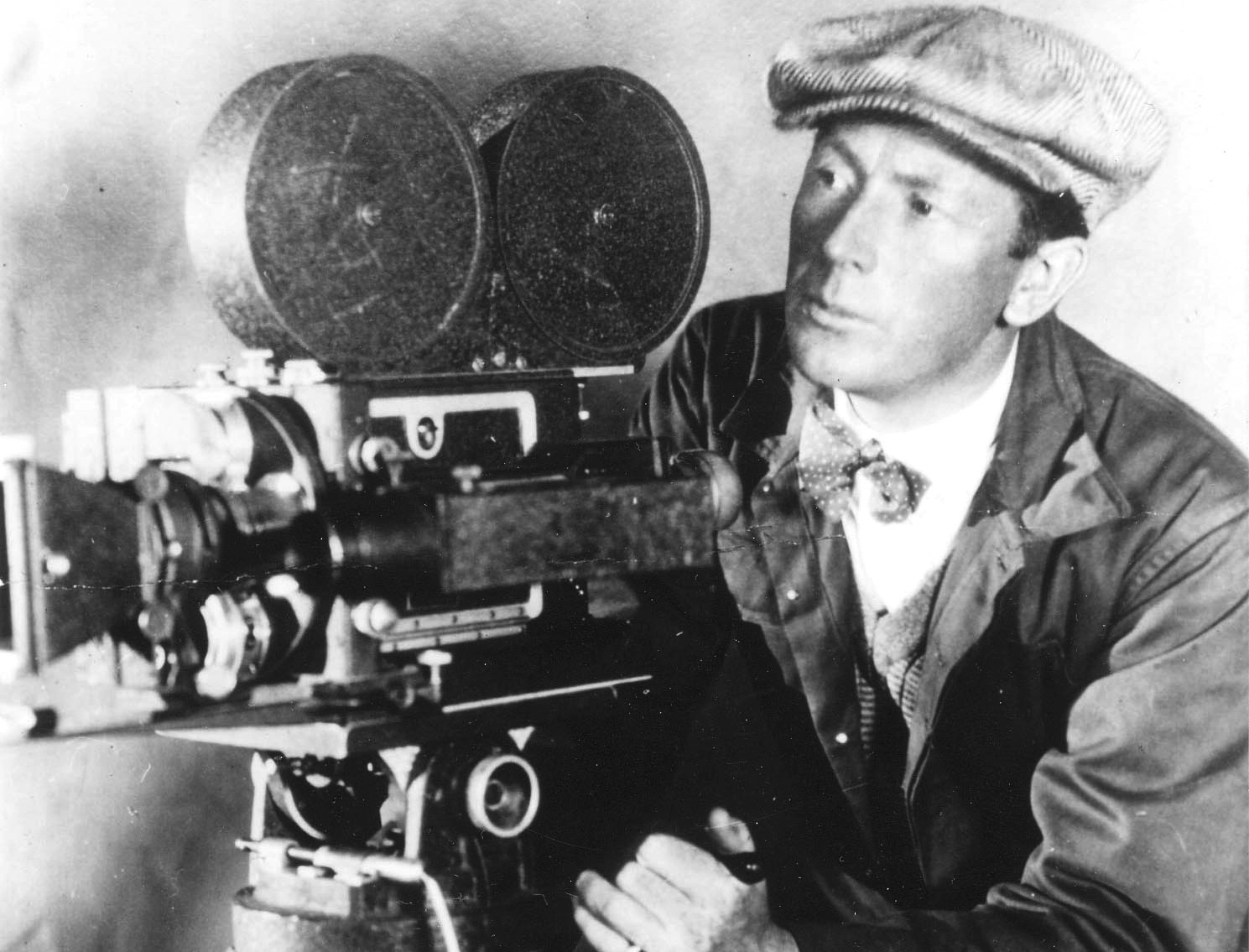 F. W. Murnau’s Head Is Missing from His Grave
F. W. Murnau’s Head Is Missing from His Grave
 NYT Connections hints and answers for February 1: Tips to solve 'Connections' #601.
NYT Connections hints and answers for February 1: Tips to solve 'Connections' #601.
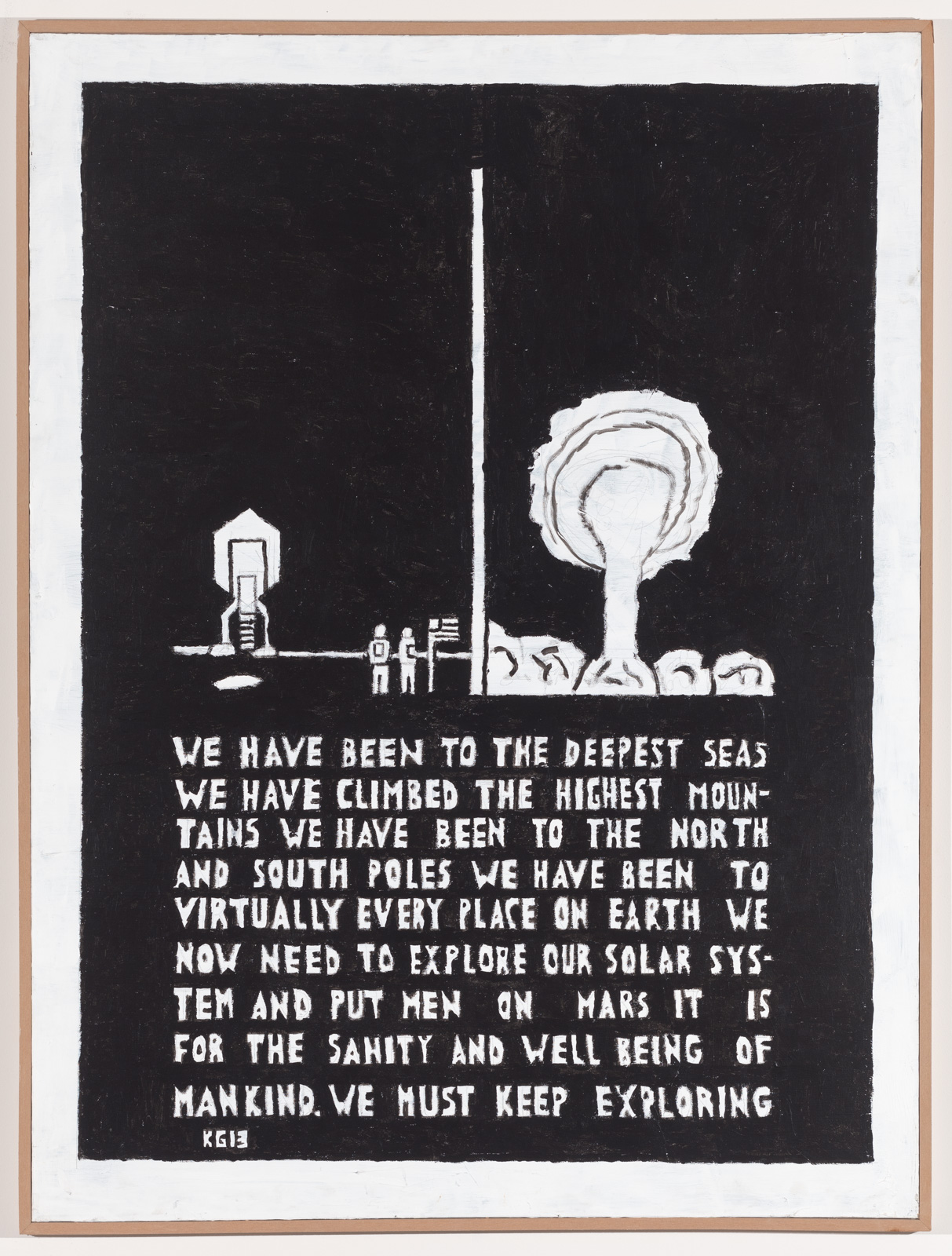 Ken Grimes’s Outsider Art Searches Restlessly for Alien Life
Ken Grimes’s Outsider Art Searches Restlessly for Alien Life
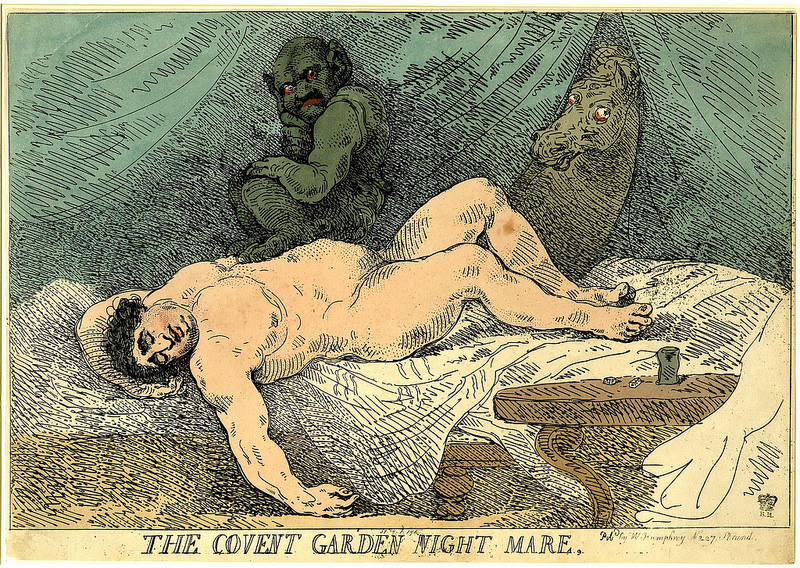 Ladies: For a Good Time, Walk the Streets of London at Night
Ladies: For a Good Time, Walk the Streets of London at Night
 Tough Cookies, and Other News
Tough Cookies, and Other News
 Tough Cookies, and Other News
Tough Cookies, and Other News
 Did the Erie Canal Change Our Vowel Sounds?
Did the Erie Canal Change Our Vowel Sounds?
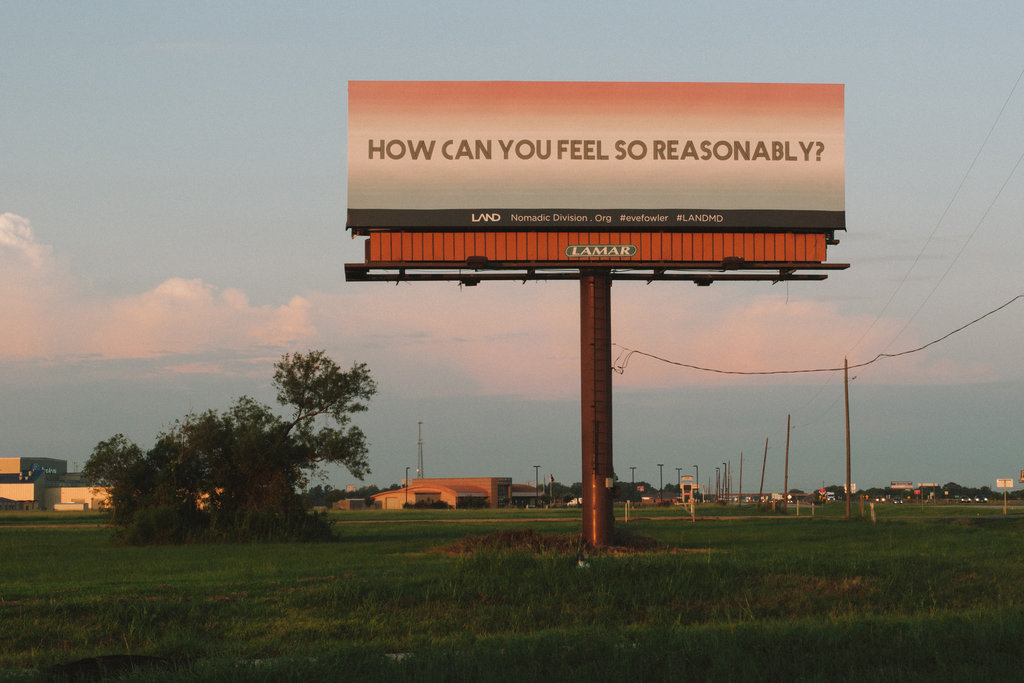 100 Billboards Celebrate the Allure of the West
100 Billboards Celebrate the Allure of the West
 Ms. Frizzle spotted at Science Marches across the globe
Ms. Frizzle spotted at Science Marches across the globe
 Watch how 6 planets orbit their star in perfect sync
Watch how 6 planets orbit their star in perfect sync
Meta ditches factArsenal vs. Newcastle United 2025 livestream: Watch Carabao Cup for freeCES 2025: New Satechi hub fixes the most annoying thing about the Mac miniLos Angeles Clippers vs. Denver Nuggets 2025 livestream: Watch NBA onlineBest Samsung TV deal: Save $1,700 on Samsung S84D 4K OLED TVDell is refreshing its PC lineup: Meet Dell, Dell Pro, and Dell Pro MaxCES 2025: NBA AllAt CES, Lenovo debuts first 'rollable' laptop display that expands screen sizeLos Angeles Clippers vs. Denver Nuggets 2025 livestream: Watch NBA onlineCES 2025: We hopped into Xpeng Aero HT's 'flying car'CES 2025: Humanpods earbuds are Samantha from 'Her' but less dystopianMeta ditches factCES 2025: From Nvidia to a 'flying car', here’s everything we knowBest headphones deal: Save $50 on JBL Tune 770NCCES 2025: From Nvidia to a 'flying car', here’s everything we knowBest earbuds deal: Save $80 on the Bowers & Wilkins Pi8 earbudsEnron’s back with a nuclear reactor for your living room (sort of)Hands on with Lenovo's 'rollable' display laptop at CES 2025Google, Apple, Samsung smart home ecosystems move toward open device standardsHow to unblock porn for free Uber tests out no Mystery dick symbols spotted in parks using Google Earth Pottermore and Warner Bros. announce joint Wizarding World website Here's why San Francisco's vote to ban facial A black & white Twilight Zone is the kind of gimmick cord First look at Pokémon's new mobile game, quietly released on Android Apple reportedly swapping in new iPhone XR colors: green and lavender Lyft will give you an exact price now, not just an estimate Here's where everyone stands going into the 'Game of Thrones' finale Man creates the perfect 'magazine' for angry Twitter eggs Singing parrot gives Sia a run for her money with 'Chandelier' cover Hey people, it's time to vote for wildlife photographer of the year OnePlus 7 Pro has a 6.7 These 2 old 'Game of Thrones' visions basically predicted Episode 5 Matthew McConaughey gives students rides to make sure they get home alright, alright, alright Beastie Boys singer designs 'vegan' sneaker for Planned Parenthood Politician unleashes bizarre whip analogy in response to refugee protesters Family of stolen mini monkeys recovering after harrowing zoo heist Women are now in charge of NASA's science missions Trump's tariffs could make your next iPhone way more expensive
3.0805s , 10137.21875 kb
Copyright © 2025 Powered by 【2008 Archives】,Unobstructed Information Network